Caddy with minimal setup
Caddy is a powerful and flexible web server that can be used to secure your Remnawave panel.
Installation
First of all, create a directory for Caddy.
mkdir -p ~/opt/remnawave/caddy && cd ~/opt/remnawave/caddy
And create a docker-compose.yml file.
touch docker-compose.yml && nano docker-compose.yml
And add the following content to the file:
services:
remnawave-caddy:
image: remnawave/caddy-with-auth:latest
container_name: 'remnawave-caddy'
hostname: remnawave-caddy
restart: always
environment:
- AUTH_TOKEN_LIFETIME=3600
- REMNAWAVE_PANEL_DOMAIN=PANEL_DOMAIN
- AUTHP_ADMIN_USER=LOGIN_USERNAME
- AUTHP_ADMIN_EMAIL=LOGIN_EMAIL
- AUTHP_ADMIN_SECRET=LOGIN_PASSWORD
ports:
- '0.0.0.0:443:443'
networks:
- remnawave-network
volumes:
- ./Caddyfile:/etc/caddy/Caddyfile
- remnawave-caddy-ssl-data:/data
networks:
remnawave-network:
name: remnawave-network
driver: bridge
external: true
volumes:
remnawave-caddy-ssl-data:
driver: local
external: false
name: remnawave-caddy-ssl-data
Configuring .env variables
Need to be set as domain for your Remnawave panel. Caddy will automatically create a certificate for this domain.
REMNAWAVE_PANEL_DOMAIN=panel.domain.com
Admin credentials. Be sure to set strong password.
AUTHP_ADMIN_USER=admin
AUTHP_ADMIN_EMAIL=[email protected]
AUTHP_ADMIN_SECRET=strong_password
Token lifetime.
AUTH_TOKEN_LIFETIME=3600
Caddyfile
Lets deep dive into the Caddyfile.
First of all, you need to select one of our predefined setups.
Full security setup with MFA
- All routes are protected by authentication. (Frontend, Backend)
- All API-endpoints are protected, includes /api/sub/* endpoints.
- Login requires MFA with OTP-codes.
- Special API-keys can be issued for /api/* endpoints.
- Full domain protection.
Run command below to download the Caddyfile.
curl -o Caddyfile https://raw.githubusercontent.com/remnawave/caddy-with-auth/refs/heads/main/examples/minimal-security-setup-with-mfa/Caddyfile
API routes without auth (api/*)
- Routes are protected by authentication. (Frontend)
- Login requires MFA with OTP-codes. (Frontend)
- All API-endpoints are not protected! (/api/* is public)
This setup exposes /api/* endpoints to the public internet.
All endpoint will no require authentication, but still using Remnawave security features.
We recommend to use full security setup with MFA for production environments with issuing API-keys.
Run command below to download the Caddyfile.
curl -o Caddyfile https://raw.githubusercontent.com/remnawave/caddy-with-auth/refs/heads/main/examples/minimal-security-setup-with-mfa-with-api-without-auth/Caddyfile
/api/sub/* endpoints without auth
- Routes are protected by authentication. (Frontend)
- Login requires MFA with OTP-codes. (Frontend)
- Only
/api/sub/*endpoints is public, other endpoints are protected.
This setup exposes /api/sub/* endpoints to the public internet.
We recommend to use full security setup with MFA for production environments with issuing API-keys and using @remnawave/subscription-page for public subscription page.
Run command below to download the Caddyfile.
curl -o Caddyfile https://raw.githubusercontent.com/remnawave/caddy-with-auth/refs/heads/main/examples/minimal-security-setup-with-mfa-with-api-without-auth/Caddyfile
Running the container
After you selected one of the setups above, you can start the container with the following command.
docker compose up -d && docker compose logs -f
Accessing the panel
After the container is running, you can access the panel at https://panel.domain.com.
After that, you will be redirected to the login page of Caddy Auth.
On the first start, you will be promted to create an MFA.
We recommend to use Google Authenticator for this.
Disable MFA
If you want to completly disable MFA, you can do this by editing the Caddyfile.
Open the Caddyfile and change the following line:
cd ~/opt/remnawave/caddy && nano Caddyfile
Find the following lines, and remove the require mfa line.
transform user {
match origin local
action add role authp/admin
require mfa
}
After that, you can restart the container with the following command.
docker compose down && docker compose up -d && docker compose logs -f
Accessing Auth Portal page
You can access the Auth Portal page at https://<your-domain>/r.
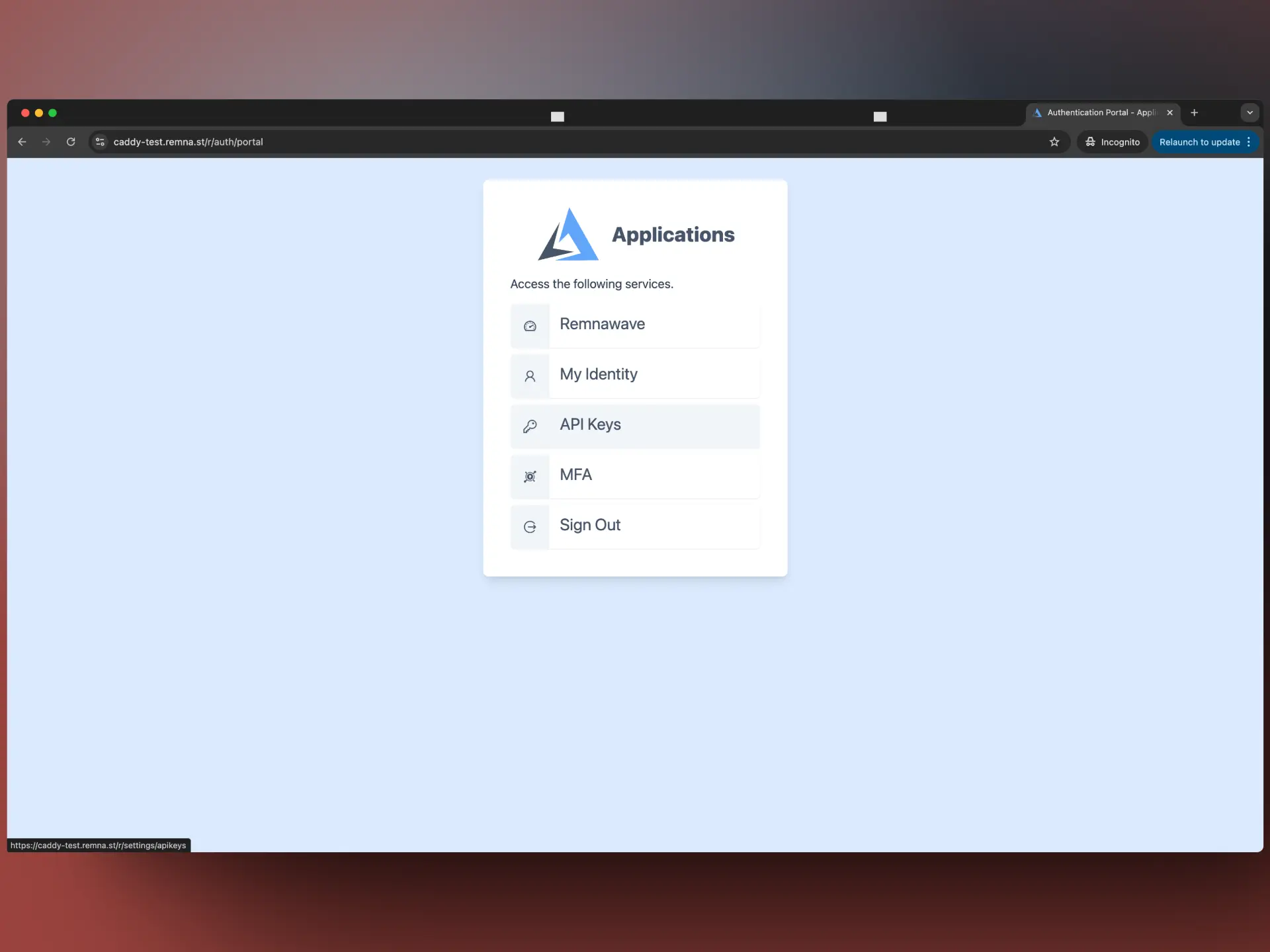
Here you can quickly go to Remnawave dashboard or manage some of Auth Portal settings.
In the MFA section, you can delete or add new MFA devices.
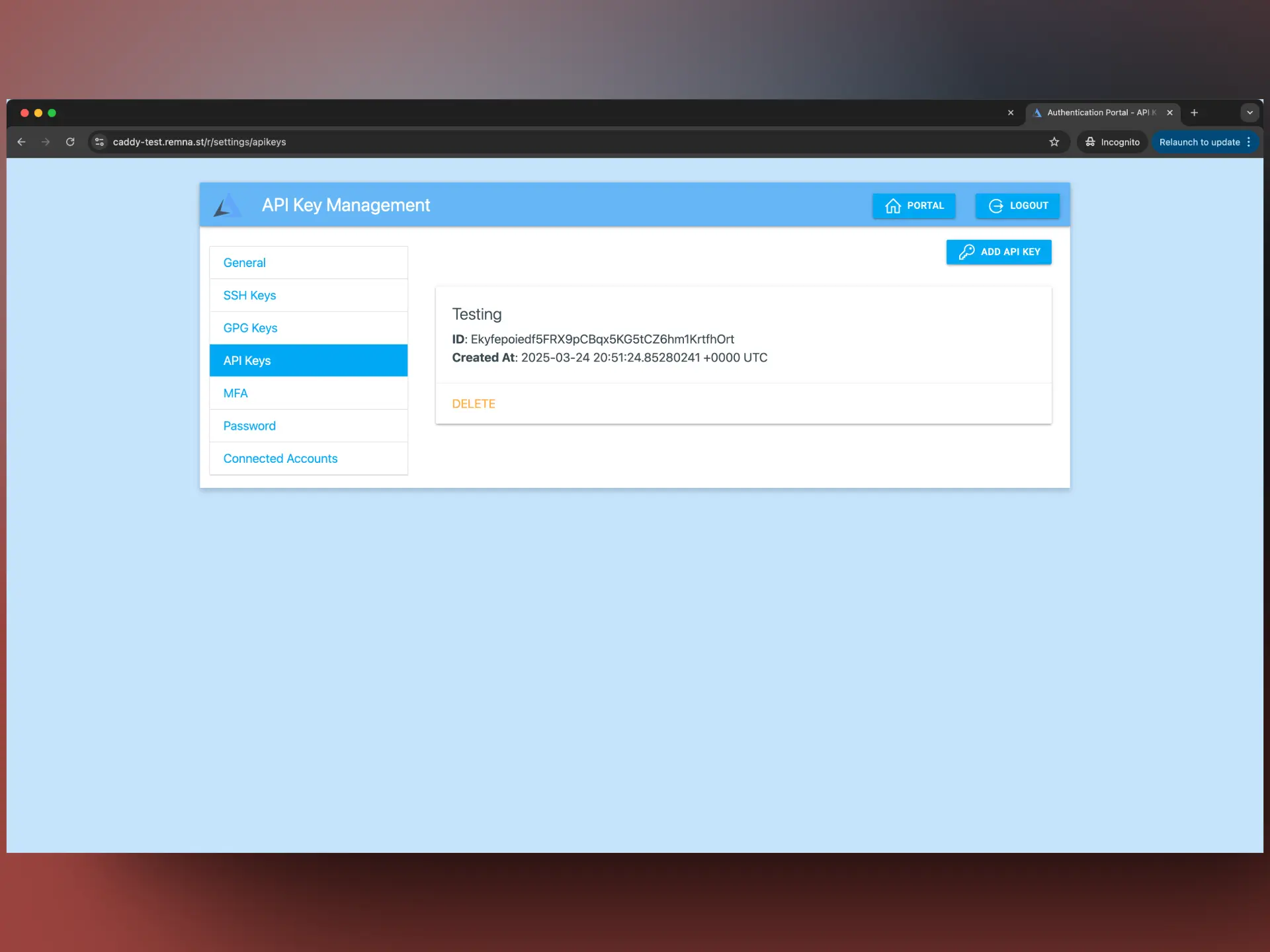
Issuing API-keys
You can access the Auth Portal page at https://<your-domain>/r.
On the Auth Portal page, you can issue API-keys, click on the API-keys tab.
After you issue an API-key, you can use it in the X-Api-Key header of your requests to the API.
Example: X-Api-Key: YxOovHLnpkcmSig5082egcHnyTk8SK4dNGAFHgZ2LKZezgj5oUj2FA2IR2sMwbALnP9YNpzZ